The messages I've received by accident have ranged from the mundane (forwarded jokes, baby pictures, nice-meeting-you-at-the-convention) to the embarrassing (think Taxicab Confessions). The first email that made me really worry about security issues, though, was from a hospital. A patient had made a mistake writing out her email address, so I ended up with correspondence that included home address, social security number, you name it. I immediately contacted the hospital to alert them of the error, and felt relieved that the information hadn't ended up in the wrong hands. I'm not sure what you'd do with the identity of someone from back-country Arkansas, but I've never wanted a credit card at Wal-Mart, either.
A few days ago I received an email asking me to confirm my email with some website called Plaxo. I'd never heard of it, so I assumed someone mistyped their email address again and deleted the message. The next day I received another email from Plaxo, then a couple more within hours. Assuming the message would keep coming, I looked for something to click on that would DISconfirm my address, but this is all the email contained:
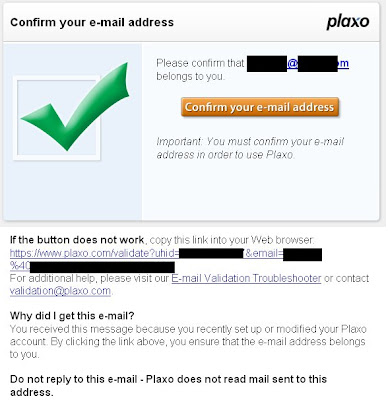
I figured my problem needed "additional help," so I sent an email to validation@plaxo.com as instructed. The next day I received this response:
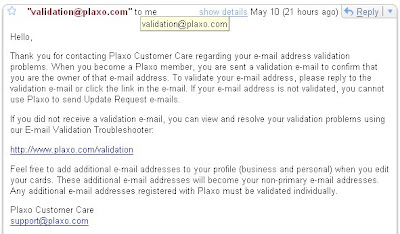
I tried to use the E-mail Validation Troubleshooter, but following the link took me to a login screen. Since it wasn't my account, I couldn't know the password, so I emailed Plaxo again, recounting my experience and telling them that there had been a mistake. The response?
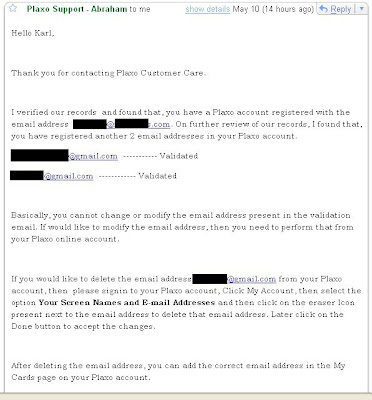
One of the three email addresses listed made it clear that their registered user's name was Kevin, but they went ahead and addressed their reply to Karl. Apparently, sending an email to validation@plaxo.com validated my email address, so now I'm anticipating a flood of emails meant to go to some guy whose typing skills leave something to be desired. I shot off yet another email to Plaxo, telling them that their confirmation process is a one-way street with no exit.
Then it hit me. If my email address had been confirmed, would I be able to claim that I had forgotten my password and get a new one sent to me? I returned to the Plaxo login screen, clicked on "Lost Password," entered my email address, and sent off the request. Within seconds, I received this:
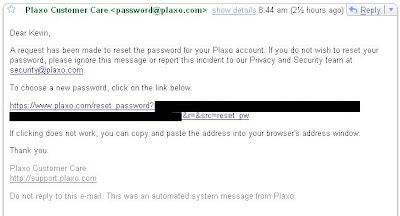
Followed the link, entered a new password, and I was in. All I wanted to do was get my email off of the account, but I could have taken whatever information I could find in this stranger's account. Scary.
This is an example of poor design leading to weak security. By not providing a way to say no to an email confirmation, anyone who received it in error could gain access to the intended user's account. Plaxo appears to be just an internet address book, but if a similar weakness existed elsewhere, a serious breach of privacy could arise. This isn't just a bad way to run a company - it's bad news for the users. Simple mistakes shouldn't lead to security lapses. Here's hoping that Plaxo can provide a bad example that others will learn by.



2 comments:
Hi Karl
Thank you for taking the time to put together this detailed post on the issue you had with Plaxo. Although this user-initiated problem is extremely rare, we still take it very seriously. Our product design and engineering groups are currently working on a solution.
In addition, we're going to have a deeper discussion at Plaxo regarding the "Confirmation email" and the whole email validation process. We should have an "out" so that anyone receiving these emails by mistake can essentially say "Wrong Guy". Resending the Confirmation email multiple times is not the answer.
Finally, we've already started retraining our support personnel to recognize this issue, and how a non-member's report of a seemingly innocent mistaken identity can result in a security breach.
Again, thanks for bringing this to our attention. In addition, should anyone reading this have security and privacy issues they want to discuss privately, I can be reached at privacy at plaxo dot com.
Redgee Capili
Director Client Services
Nice post. Thanks.
Post a Comment